- FIND LABELS BY:
- Use Case
- Warehouse Management
-
-
- Warehouse Rack LabelsDurable, fully customized label options for every warehouse rack system, including long-range scanning.
- Warehouse Floor Label KitsThe most durable bar code labeling solutions available, with permenant adhesive or mechanical attachment options.
- Warehouse SignsBrowse location, identification and safety signage for both indoor and outdoor installation.
- Warehouse Cold StorageCheck out labels and signs that can be installed in refrigerated or freezing warehouse environments as cold as -20°F.
- Bulk Storage LabelsDesigned to withstand abuse from forklifts and the inclement conditions of both warehouse environments and the outdoors.
- Outdoor SolutionsExplore labels and signs engineered to last in even the outdoor spaces.
-

-
Maximize efficiencies across your warehouse with a customized warehouse labeling system.
When setting up a new Warehouse Management System (WMS), you want rack labels printed correctly and ready for easy, accurate installation. Get the most out of your WMS investment with durable, customizable warehouse labels and signs. Need help? Get in Touch ›
-
-
- CMMS Maintenance Management
-
-
- Utility & Energy Maintenance TrackingExplore durable asset tracking tag options for utilities and energy applications.
- Telecom AssetsExplore telecommunication asset tracking options.
- Government & Civil AssetsExplore asset tags designed for permanent attachment to government assets such as traffic signs, equipment and infrastructure.
- Manufacturing AssetsExplore asset tags designed to last in harsh manufacturing conditions.
-

-
Track and maintain your assets to keep operations running smoothly.
Durable asset tags connect your equipment with your CMMS or FM software package. Set up your program correctly the first time with properly designed tags that last in your conditions and integrate properly with your software application(s). Need help? Get in Touch ›
-
-
- Inspection & Audit Tracking
-
-
- Leak Detection & Repair (LDAR)Explore asset tags designed for fugitive emissions program asset identification and tracking.
- Traffic Sign Retroreflectivity (RRF)Explore durable asset tags for tracking traffic signs and other infrastructure assets.
- Gas Cylinder TestingIncrease the accuracy of cylinder tracking for testing, certification and delivery.
- Cable Tracking & TestingLabels designed specifically for cable or hose applications requiring a durable bar code label.
-

-
Automate and error-proof your asset inspection process.
Uniquely and permanently identify equipment your teams need to inspect or maintain in the field to automate inspections and virtually eliminate the chance inspections are done on the wrong asset. Need help? Get in Touch ›
-
-
- Facilities Management
-
-
- Commercial Real EstateExplore asset identification and tracking labels for commercial real estate
- EducationExplore asset tags designed for educational facilities and university property tracking.
- Government & Civil AssetsExplore asset tags designed for permanent attachment to government assets.
- HealthcareExplore asset tags for hospital facilities, medical device tracking and sterile assets.
-
- Property Identification TagsExplore options for easy identification and tracking of property assets.
- RetailExplore asset identification and tracking labels for the retail market.
- Asset Management Control PortalEasily standardize asset management across your entire organization with a dedicated online asset label portal.
-
-
- Manufacturing WIP Tracking
-
-
-
-
Work In Process Asset Tracking Tags.
Explore asset tags designed for tracking work-in-process items during the manufacturing process. Need help? Get in Touch ›
-
-
-
- Compliance Marking
-
-
-
-
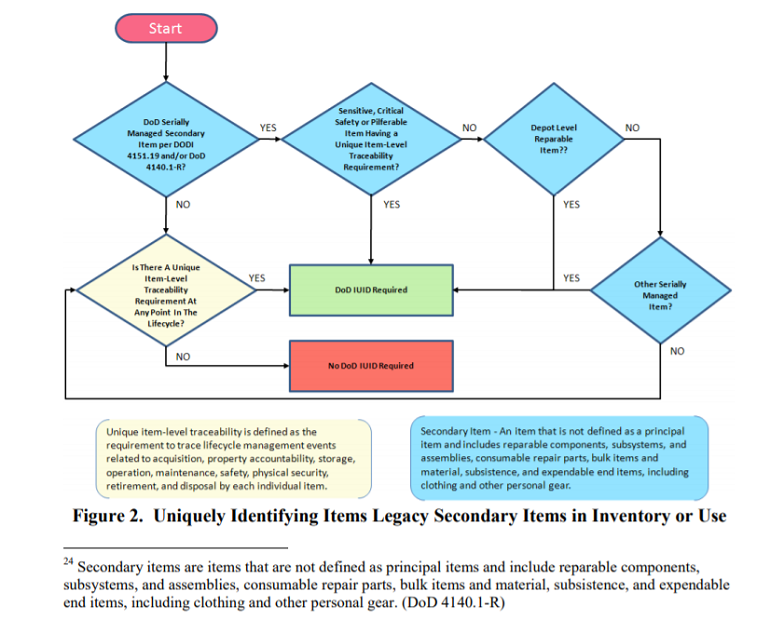
Ensure compliance with any asset management standard.
Many government, military and original equipment manufacturers (OEMs) require their suppliers to mark in accordance with a specification or standard. Need help? Get in Touch ›
-
-
-
- Harsh Environment Tracking
-
-
- Sunlight/UV & WeatherExplore asset tags certified for installation in outdoor environments exposed to sunlight, weather and heat.
- High TemperaturesExplore heat-resistant labels that withstand temperatures up to 1,200°F.
- Chemical ResistanceExplore labels resistant to degredation from exposure to a wide variety of solvents, cleaners and other chemicals.
- SaltwaterExplore asset tags for use in marine operating conditions exposed to saltwater spray.
- Abrasion & High TrafficExplore asset tags for use in abrasive conditions such as harsh industrial, desert or high-traffic applicaitons.
-

-
Get continuous asset tracking, even in the harshest conditions.
See why asset managers trust Metalphoto photosensitive anodized aluminum in applications where permanent identification is critical. Need help? Get in Touch ›
-
-
- Security Labels
-
-
-
-
Security Labels and Tamper-Evident Barcode Labels.
Explore tamper-evident and anti-counterfeit asset tracking barcode labels. Need help? Get in Touch ›
-
-
-
- Consumer Product Tracking
-
-
-
-
Consumer Product Registration & Tracking Labels.
Durable, QR code labels that enable product tracking and easy product registration for consumers. Need help? Get in Touch ›
-
-
-
- General Asset Tracking
-
-
- Industrial Metal Barcode Labels, Tags and StickersAsset identification with tracking options featuring unmatched durability for industrial environments.
- Property Identification TagsExplore options for easy identification and tracking of property assets.
- Durable Labels and Tags for Harsh Industrial EnvironmentsExplore barcode labels designed for permanent tracking of assets installed in harsh operating conditions.
-
- Firearm TrackingExplore durable firearm tracking options that increase accountability and enable compliance.
- Gas Cylinder & Tote TrackingExplore barcodes designed to permanently track gas cylinders and chemical totes.
- Utility Asset LabelsExplore durable asset tracking tag options for electric, gas and water utilities.
-
-
- On-Site Label Making
-
-
-
-
On-Demand Metal Label Manufacturing System.
When you need to produce labels or nameplates in real-time, Camcode’s all-in-one On-Demand Laser System provides you with everything you need create them quickly and easily. Need help? Get in Touch ›
-
-
-
- Warehouse Management
- Industry
- Defense & Law Enforcement
-
-
- UID LabelsExplore tracking options that comply with Unique Item Identification (UID) standards such as MIL-STD-130 (USA) and STANAG 2290 (NATO).
- Firearm TrackingExplore durable firearm tracking options that increase accountability and enable compliance.
- On-Demand Metal Label Manufacturing SystemProduce durable, ready-to-apply barcode labels where and when needed with Camcode’s On-Site/On-Demand Laser Marking System
- RFID LabelsExplore radio-frequency identification (RFID) asset tags.
-

-
Labels that meet defense standards and last the life of your assets.
Track property, manage preventive maintenance, reduce operational costs, and more with UID labels that meet an array of government, industrial and military specifications including MIL-STD 130. Need help? Get in Touch ›
-
-
- Education
-
-
-
-
Label and track your education organization’s property with durable barcode labels.
Serialized asset tags that have the durability to last the life of your education items. Our barcode labels integrate seamlessly into the leading education asset tracking software solutions and virtually eliminate errors caused by manual data collection, ensuring accurate information. Need help? Get in Touch ›
-
-
-
- Utility & Energy
-
-
- UtilityExplore durable asset tracking tag options for utility assets and equipment.
- EnergyExplore durable asset tracking tag options for assets and equipment in power generation applications.
- Gas UtilityExplore durable asset tracking tag options for natural gas production and distrbituion assets and equipment.
- Oil and GasExplore durable equipment tracking tag options for oil and gas exploration, production and distribution.
- Bar Code Tags for Utility Pole ApplicationsSee how barcoded utility pole tags can automate mainteance, inspection and joint-use tracking.
-

-
Efficient asset management systems begin with Camcode bar code labels.
From meter tags used for meter maintenance systems to pole tags used to track inspection and treatment, utilities rely on Camcode’s highly durable anodized aluminum bar code labels. Need help? Get in Touch ›
-
-
- Government & Civil
-
-

-
Improve tracking and minimize risk with labels that last the life of your assets
Camcode asset tags are designed for permanent attachment a wide variety of government fixed-asset inventory items such as office equipment to outdoor street signs. Need help? Get in Touch ›
-
- Healthcare
-
-

-
Durable asset tracking labels for the healthcare industry.
With durable medical asset tracking labels, you’ll reduce replacement costs, integrate seamlessly with asset management solutions, and eliminate manual data entry errors. Need help? Get in Touch ›
-
- Heavy Equipment
-
-
-
-
Reduce replacement costs and integrate seamlessly with durable asset tracking labels.
Construction, farming and mining equipment can see a lot of abuse. When tracking heavy equipment and its components, select an asset tag that is durable enough to last (and stay affixed) for the life of the equipment/component. Need help? Get in Touch ›
-
-
-
- Manufacturing
-
-

-
Labels that last the life of your manufacturing assets.
Manufacturers discovered long ago that Camcode asset tags and nameplates offer extremely durable asset identification and can be delivered quickly and cost-effectively. Need help? Get in Touch ›
-
- Shipboard & Marine
-
-

-
Modernizing shipboard marking.
Camcode’s broad experience in the identification products market and with ship marking are unique in the industry. Camcode produces millions of custom identification products every year and has traveled to over 250 sites worldwide to assess and mark equipment items. Need help? Get in Touch ›
-
- Telecommunications
-
-
-
-
Automate and error-proof your asset tracking processes.
Camcode barcode pole tags virtually eliminate errors caused by manual data collection, ensuring accurate information. This improves the productivity and effectiveness of a telecommunications company by reducing entry errors in the field. The results are increased revenue, lower expense and better management of risk and NESC requirements. Need help? Get in Touch ›
-
-
-
- Warehouse / Logistics
-
-
- Warehouse Rack LabelsDurable, fully customized label options for every warehouse rack system, including long-range scanning.
- Warehouse Floor Label KitsThe most durable bar code labeling solutions available, with permenant adhesive or mechanical attachment options.
- Warehouse SignsBrowse location, identification and safety signage for both indoor and outdoor installation.
- Warehouse Cold StorageCheck out labels and signs that can be installed in refrigerated or freezing warehouse environments as cold as -20°F.
- Bulk Storage LabelsDesigned to withstand abuse from forklifts and the inclement conditions of both warehouse environments and the outdoors.
- Outdoor Warehouse SolutionsExplore labels and signs engineered to last in even the outdoor spaces.
-

-
Make it easy for workers to navigate the facility, cut down on travel time & congestion in aisles.
You can streamline picking & stocking processes and remove the guesswork of identifying the proper storage locations for inventory. Need help? Get in Touch ›
-
-
- Defense & Law Enforcement
- Environment
- Weather and Sunlight
-
-
-
-
Durable labels for sunlight and UV exposure.
Standard asset labels don’t surive extended outdoor exposure. For assets exposed to outdoor conditions, Camcode recommends Metalphoto® photosensitive anodized aluminum. Need help? Get in Touch ›
-
-
-
- Ultra-High Temperatures
-
-
-
-
Labels with ultimate heat-resistance.
Anodized aluminum face stock labels that are trated with our proprietary XHT process to withstand exposure to temperatures up to 1200°F. Need help? Get in Touch ›
-
-
-
- Chemical Resistance
-
-
-
-
Camcode offers several chemical resistant asset label materials.
Whether it’s hydraulic fluid, jet fuel, gasoline or a wide variety of industrial solvents, cleaners and acids, Camcode has a variety of asset tracking label materials that will remain scannable after prolonged chemical exposure. Need help? Get in Touch ›
-
-
-
- Saltwater
-
-
-
-
Proven saltwater resistance for asset tracking in marine applications
Asset tags used in ocean environments must be resistant to corrosion from salt spray. Camcode has worked with offshore oil rigs, shipping containers, Naval vessels, and ports around the world to tag and track assets deployed on or near the ocean. Need help? Get in Touch ›
-
-
-
- Abrasion & High Traffic
-
-
-
-
Labels with engineered, proven abrasion resistance.
Asset tags in harsh industrial, desert or high-traffic public environments can be exposed to abrasive conditions that will render most standard asset tags unreadable. Select an asset tracking label that is proven to survive abrasive conditions. Need help? Get in Touch ›
-
-
-
- Weather and Sunlight
- Material
- Metalphoto®
-
-
-
-
Trusted for over 50 years by The US Armed Forces, NASA, Caterpillar and Boeing.
The most durable printed aluminum substrate available, ideal for prolonged exposure to the harshest outdoor environments. The durability for which Metalphoto is known is the result of a unique manufacturing process in which a silver halide image is embedded within the sapphire-hard, anodic layer of the aluminum. Need help? Get in Touch ›
-
-
-
- DuraBlack®
-
-
-
-
DuraBlack® durable laser-markable aluminum for CO2 lasers.
Label blanks made of the most durable CO2 laser markable aluminum substrate on the market, ready to mark onsite and available with several attachment options. Need help? Get in Touch ›
-
-
-
- AlumaMark®
-
-
-
-
AlumaMark® CO2 laser-markable aluminum.
Label blanks made of the only CO2 laser-markable aluminum that produces black graphics on a natural background. Available with several attachment options. Need help? Get in Touch ›
-
-
-
- Teflon™ Metalphoto®
-
-
-
-
Teflon™ coated Metalphoto® barcode labels.
Camcode’s Metalphoto with Teflon is perfect for applications that require resistance to paint (including CARC) or contact with strong acids or caustics. Need help? Get in Touch ›
-
-
-
- XHT Metalphoto®
-
-
-
-
Metalphoto XHT (Extra High Temperature) labels.
Anodized aluminum face stock labels that are trated with our proprietary XHT process to withstand exposure to temperatures up to 1200°F. The photographic-quality bar code and graphic images are sealed within the anodic layer of the aluminum, creating a very durable, high-quality and temperature-resistant metal asset tag. Need help? Get in Touch ›
-
-
-
- BlackPLUS™
-
-
-
-
AlumaMark® BlackPLUS™ laser markable aluminum.
AlumaMark BlackPLUS is the most durable YAG/Fiber laser-markable aluminum on the market. This label is constructed of aluminum with an inorganic black colorant with satin finish, displaying silver graphics on a black background. Need help? Get in Touch ›
-
-
-
- Stainless Steel
-
-
-
-
304 alloy or 316 alloy stainless steel.
Designed specifically for applications requiring resistance to frequent cleaning with strong caustics, such as food processing, medical, laboratory, chemical, textile, petroleum and marine environments. Need help? Get in Touch ›
-
-
-
- Brass
-
-
-
-
Brass labels and tags with a rich luster and striking appearance.
A popular choice for industrial and decorative applications, a robust and malleable metal that performs well in indoor and outdoor environments, offering excellent resistance to saltwater, corrosion, tarnish, chemicals and solvents, as well as extreme temperatures. Need help? Get in Touch ›
-
-
-
- tesa® Tape
-
-
-
-
tesa® Secure™ bar code labels for MIL-STD-130.
These poly-acrylic labels are strong yet flexible in many conditions, and feature UV resistance with a tamper-proof design. Need help? Get in Touch ›
-
-
-
- Polyester
-
-
-
-
Premium polyester asset labels.
Durable gloss white polyester labels with permanent pressure sensitive adhesive to clearly mark and identify indoor assets, such as office equipment. Need help? Get in Touch ›
-
-
-
- Vinyl
-
-
-
-
Vinyl asset labels and tags.
Aneconomical plastc label option with superior pliability, performing well for interior labeling applications. Need help? Get in Touch ›
-
-
-
- RFID
-
-
-
-
RFID asset labels and tags.
Radio Frequency Identification (RFID) tags are an ideal asset tracking system in certain applications, however before investing, consider the functionality, durability and security issues of RFID. Need help? Get in Touch ›
-
-
-
- Metalphoto®
- Certification
- All Certifications & Specifications
-
-
-
-
Metalphoto® is field proven to last over 20 years and meet the most demanding specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including MIL-STD-130 for Department of Defense UID data matrix bar code applications. Need help? Get in Touch ›
-
-
-
- GG-P-455B
-
-
-
-
Federal Specification
GG-P-455B(3)This specification covers the requirements for photosensitive anodized aluminum sheets and foils. Need help? Get in Touch ›
-
-
-
- MIL-STD-130
-
-
-
-
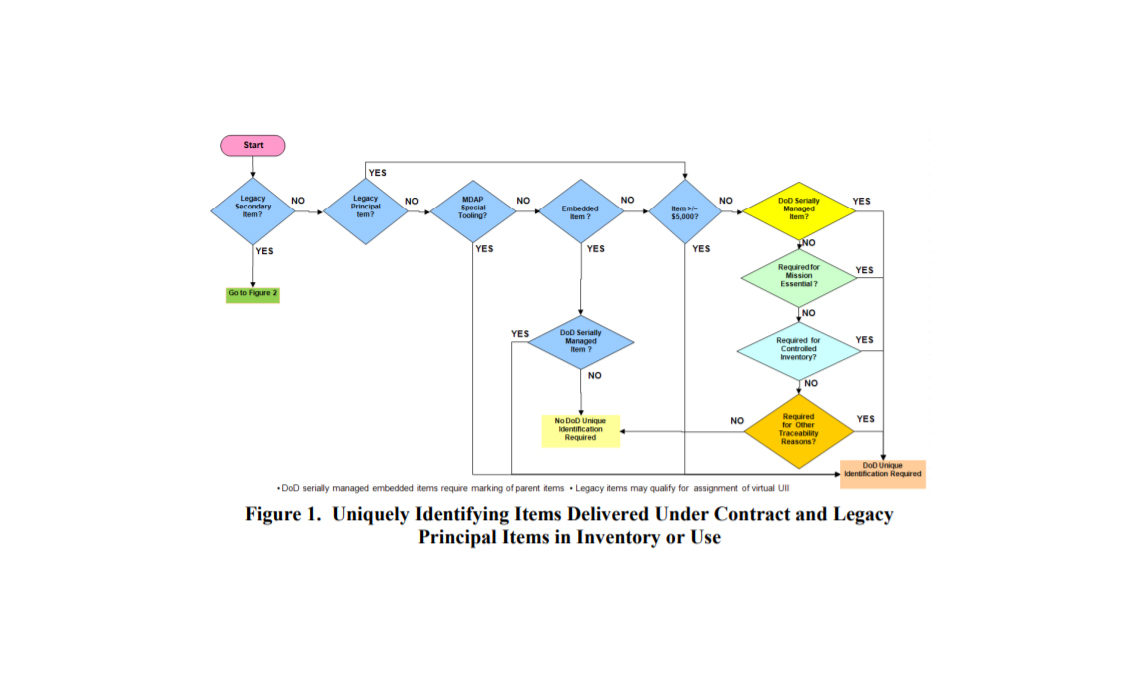
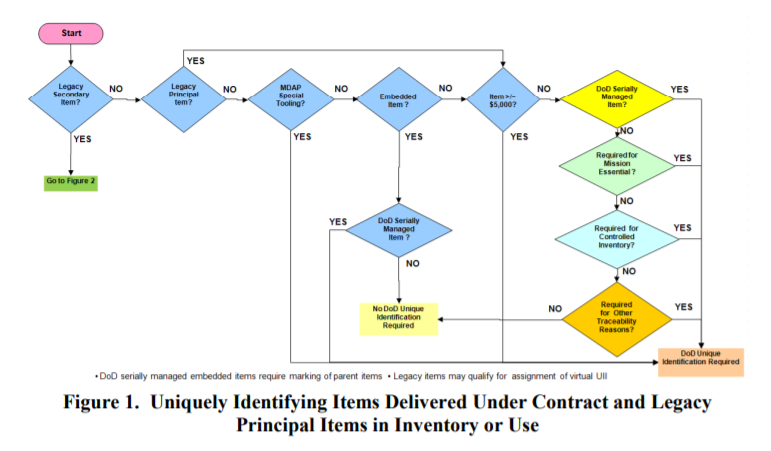
Military Standard 130
(MIL-STD-130)One of many standards that the U.S. Government has developed to guide individuals and companies within the DoD and outside the DoD on uniform engineering and technical requirements for military-unique or substantially modified commercial processes, procedures, practices, and methods. Need help? Get in Touch ›
-
-
-
- STANAG 2290
-
-
-
-
Standardization Agreement
(STANAG) 2290Provides details on both the construction of the UII and the marking of items with a UII. Need help? Get in Touch ›
-
-
-
- UL PGGU2
-
-
-
-
Underwriters Laboratories (UL)
UL PGGU2Provides details on the viability of using Metalphoto for marking and labeling system material components. Need help? Get in Touch ›
-
-
-
- Lockheed Martin
-
-
-
-
Metalphoto® meets Lockheed Martin UID specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including Lockheed Martin UID specifciations. Need help? Get in Touch ›
-
-
-
- Boeing
-
-
-
-
Metalphoto® meets Boeing industry specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including Boeing Commercial Aircraft Company specifciations. Need help? Get in Touch ›
-
-
-
- Honeywell
-
-
-
-
Metalphoto® meets Honeywell industry specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including Honeywell, Inc. industry specifciations. Need help? Get in Touch ›
-
-
-
- BF Goodrich Aerospace
-
-
-
-
Metalphoto® meets BF Goodrich aerospace specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including BF Goodrich aerospace specifciations. Need help? Get in Touch ›
-
-
-
- SAE
-
-
-
-
Metalphoto® meets SAE specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including SAE industry specifciations. Need help? Get in Touch ›
-
-
-
- NASA
-
-
-
-
Metalphoto® meets NASA identification specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including NASA identification specifciations. Need help? Get in Touch ›
-
-
-
- CSA
-
-
-
-
Metalphoto® meets CSA identification specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including Canadian Standard Association (CSA) identification specifciations. Need help? Get in Touch ›
-
-
-
- NATO
-
-
-
-
Metalphoto® meets NATO identification specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including NATO identification specifciations. Need help? Get in Touch ›
-
-
-
- US Department of Defense
-
-
-
-
Metalphoto® meets US DOD identification specifications.
Metalphoto satisfies wide ranging set of industrial, government and military specifications including US Department of Defense identification specifciations. Need help? Get in Touch ›
-
-
-
- All Certifications & Specifications
- EXPLORE
- Create My Own Labels
- Services
- Blog
- Contact Us